Smart Home Security Tips
Estimated reading time: 7 minutes
One of the top reasons that people site when asked why they are not keen on adopting smart home technology is security. There is a natural wariness about who has access to your data and how easy it might be for someone to enter your home through the internet connection to the devices you own. This fear is not helped by some high profile cases where baby monitors and security cameras have been hacked, giving criminals the ability to see inside the home. And other cases where video feeds from another customers account have accidently been shared to the wrong customer.
In this blog we’ll share our tips for making your smart home more secure, some of which overlap with general good practice when it comes to protecting your home network, including computer and laptop devices.
While you can never 100% guarantee security, there are ways that you can reduce the likelihood by adding additional safeguards to prevent and put off hackers.
About Our Blog
We live in an ageing society. But what does that really mean?
In the next 20 years the balance of young and old will shift to the point where there will be one elderly person for every two people of working age. The challenge this presents is two-fold, a reduction in family members able to provide support and a smaller pool of professional carers.
TL Tech is a Smart Homes Solutions provider with a difference. We help people get the best out of smart home technologies and create unique home environments to meet their needs and budget. Our vision is to “create a home that cares for you as you age”.
Smart home technologies have the power to transform lives, especially for the vulnerable in our society. This blog series will be looking to showcase the opportunities, find out more about the people working in this field and how we can create a world where “smart meets kind ®”.
General Cyber Security
In many ways smart home security is no different to the security measures you should be putting in place to protect your home computer and tablet devices.
We recommend to start with the government National Cyber Security Centre (NCSC) guidance on their website at https://www.ncsc.gov.uk/cyberaware/home
This will help you improve your knowledge of cyber security and the steps are clearly described to help you implement them.
Here they share six top tips:
- Create a separate password for your email
- Use strong passwords using three random words
- Save your passwords in your browser
- Turn on two-factor authentication (where available)
- Update your devices
- Turn on backup (and do this regularly)
Cyber Security for the Smart Home
There are three main areas of weakness to consider when it comes to smart home security, the first is the network that the devices are connected to, the second is mobile devices such as phones/laptops/tablets if you use these to view and control devices in the home and the last is the smart devices themselves. We will first talk about home networks and the things that you should consider, move on to mobile devices and then provide some guidance for any smart devices that you may have, or may be considering investing in.
Note that the guidance that follows is generic and you should always follow the manufacturer’s handbooks or website support guides for your specific make and model of device to make sure that the security settings are correct.
There are other more complex aspects such as data encryption which we have not covered within this guide.
Home Networks
We recommend updating the default username and password on your router. This is a good way to put off hackers, making it harder for them to guess the access credentials.
Check if your router has a firewall and if not set up or activate the firewall on your router.
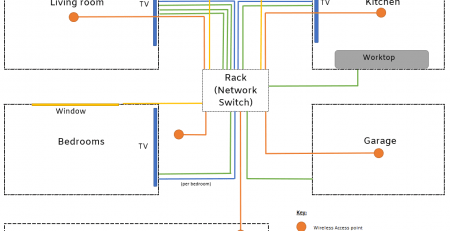
If possible. create a second network on your router for the smart-home devices separate from the primary network your computers are on. Then at least if a hacker does gain access to your smart home, they will not be able to access your sensitive information on your home computer. It’s also a good idea to set up a guest network for visitors to keep their devices completely separate from yours.
Mobile Devices (such as Laptops, Phones and Tablets)
Make sure that all your computers are password protected. Use a strong password, see earlier advice from the NCSC on managing passwords. We recommend LastPass for storing passwords across all your devices, it also has a password generator feature for creating random passwords with a mixture of letters, numbers, upper/lower case and special characters.
On mobile phones and tablets set up the lock screen with access restricted unless the passcode, finger print or facial recognition are used.
Be wary of logging on to public Wi-Fi with your phone, laptop or tablet. If you don’t need authentication to get into a network, neither do hackers. Often these networks have hidden small print that gives them access to data on your device in return for the “free” internet access, so you should try to avoid using these services. You might want to consider using a Virtual Private Network (VPN) secure connection to protect your devices.
Smart Devices
It is important to do your research when it comes to choosing devices.
- Check if there are any inherent weaknesses in the design. Is access restricted through passwords, two-factor authentication (2FA), or multi-factor authentication (MFA)?
- How good is the company at identifying and addressing security issues in a timely manner?
- Is software maintained and able to be updated? Is this automatic or does the device owner need to check and perform these updates manually?
Passwords
Many devices come set with a default password, which is often very basic and easy to guess, or may have been shared on the internet. You should change this when you first set up the device to a strong password.
Device Updates
Register every new device with the manufacturer so that you are on their mailing list for any important update information or security concerns. Keep a note of these, so that if you change contact details (such as email address), you know who you need to provide new details to. Staying up-to-date with software is important as often these updates are released to address potential security vulnerabilities.
Device Hardware
Be wary of devices that are physically accessible from outside of the home, such as doorbells, cameras and garage door openers that could be tampered with or manually reset. This is another way that someone can maliciously gain access to your smart home. This goes back to doing your research and finding out how manufacturers design their systems to protect against physical tampering.
Factory Reset
If you are getting rid of any devices, you must always perform a factory reset to make sure that all of your data is wiped from the device. You can see a guide here of how to do this.
Key Takeaways
We know that technology can be daunting for some and it might be easy to forget about as it’s often not visible. Unfortunately the cyber world is full of potential attackers looking for weaknesses and it is important to implement these steps that we have shared to protect not only your smart home devices, but the other interconnected devices. If you only do one thing, changing the default password on your router and devices will go a long way to protect your home.
If you have any issues at all with strengthening the security on your home network, or would like some further advice on smart home device security, then we would be happy to help guide you. If your smart home includes a voice assistant, we have also prepared a guide on managing your data privacy with Amazon Alexa.
If you try any of our tips it would be great to hear your stories. Perhaps you have a favourite smart home security tip that you would like to share. Do get in touch as we’d love to hear your thoughts on how you feel about smart homes and what you would like to see the industry provide to ensure that your privacy is protected and to strengthen data security.
You can also check out our website for more technical advice or subscribe to our mailing list to be notified when we have new posts and support material available.







Comments (2)
Your blog about Smart Home Security Tips is an amazing blog. It is filled with rich info. Thanks a lot for sharing such a wonderful blog.
You’re welcome, thanks for commenting.